-
Type:
Public Security Vulnerability
-
Resolution: Fixed
-
Priority:
Low
-
Affects Version/s: 4.20.0, 4.20.1, 4.20.2, 4.20.3, 4.20.4, 4.20.5, 4.20.6, 4.20.7, 4.20.8, 4.20.9, 4.20.10, 4.20.11, 4.20.12, 4.20.13, 4.20.14, 4.20.15, 4.20.16, 4.20.17, 4.20.18, 4.20.19, 4.20.20, 4.20.21, 4.20.22, 4.20.23, 4.20.24, 4.21.0, 4.21.1, 4.22.0, 4.22.1, 4.22.2, 4.22.3, 4.22.4, 4.22.5, 4.22.6, 5.3.0, 5.4.0, 5.4.1, 5.4.2, 5.4.3, 5.4.4, 5.4.5, 5.4.6, 5.4.7, 5.4.8, 5.6.0, 5.7.0, 5.7.2, 5.8.1, 5.9.0, 5.9.1, 5.10.0
-
Component/s: None
-
7.5
-
High
-
CVE-2022-25647
-
Atlassian (Internal)
-
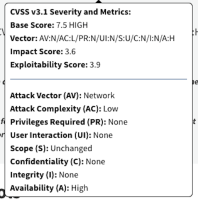
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H
-
Patch Management
-
Jira Service Management Data Center, Jira Service Management Server
This High severity Third-Party Dependency vulnerability was introduced in version 4.20.0 of Jira Service Management Data Center and Server.
This vulnerability, with CVSS Score(s) of 7.5, and CVSS Vector(s) of CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H, allows an unauthenticated attacker to expose assets in your environment susceptible to exploitation which has no impact to confidentiality, no impact to integrity, high impact to availability, and requires no user interaction
Atlassian recommends that Jira Service Management Data Center and Server customers upgrade to latest version, if you are unable to do so, upgrade your instance to one of the specified supported fixed versions:
- Jira Service Management Data Center and Server 4.20: Upgrade to a release greater than or equal to 4.20.25
- Jira Service Management Data Center and Server 5.4: Upgrade to a release greater than or equal to 5.4.9
- Jira Service Management Data Center and Server 5.9: Upgrade to a release greater than or equal to 5.9.2
- Jira Service Management Data Center and Server 5.10: Upgrade to a release greater than or equal to 5.10.1
See the release notes (https://confluence.atlassian.com/servicemanagement/jira-service-management-release-notes-780083086.html). You can download the latest version of Jira Service Management Data Center and Server from the download center (https://www.atlassian.com/software/jira/service-management/download-archives).
The National Vulnerability Database provides the following description for this vulnerability: The package com.google.code.gson:gson before 2.8.9 are vulnerable to Deserialization of Untrusted Data via the writeReplace() method in internal classes, which may lead to DoS attacks.