-
Type:
Suggestion
-
Resolution: Unresolved
-
Component/s: REST API
-
Jira Software
Issue Summary
When calling the Automation Rule Management REST API in Jira Cloud, the response returns the complete rule configuration, including sensitive values (e.g. authorization headers, API tokens, webhook URLs) in clear text.
The UI masks such fields, but the API does not, allowing any user with permission to call the API to read these secrets.
Steps to Reproduce
Step 1
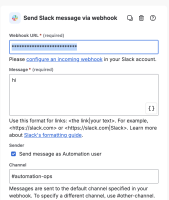
In a Jira Cloud site, create or edit an Automation rule that uses sensitive values directly in the rule configuration. For example:
- Add a “Send web request” action with:
- A webhook URL containing a secret token, or
- An Authorization header with an API key / bearer token.
- Save and publish the rule.
Step 2
Use a user account that has permission to manage automation rules (typically a global admin) and an API token to call the Automation Rule Management API:
GET
https://api.atlassian.com/automation/public/{product}/{cloudid}/rest/v1/rule/{ruleUuid}
Authorization: Bearer <API_TOKEN>
Accept: application/json
(Replace {product}, {cloudid}, and {ruleUuid} with the appropriate values for the Cloud site and rule.)Observe the JSON response.
Expected Results
The API should not expose sensitive values in clear text. At minimum, sensitive fields (e.g. authorization headers, tokens in URLs) should:
- Be masked, or
- Be omitted, or
- Be replaced with placeholders, in line with the masking behavior seen in the UI.
Alternatively, the API should provide a “safe export” mode or parameter that returns a redacted configuration suitable for backup/promotion use, without leaking secrets.
Actual Results
The API response includes the full raw configuration of the rule, including:
- Webhook URLs with embedded tokens.
- Authorization header values (API keys / bearer tokens).
- Any other secrets entered directly into rule fields.
These values are returned in clear and unencoded text, unlike in the UI where sensitive fields are visually masked.
Any user with sufficient permission to call this API (e.g. global admin with an API token) can retrieve all such secrets from automation rules, making it unsafe to use the API for export/backup without manual or custom redaction.
Workaround
Currently there is no known workaround for this behavior. A workaround will be added here when available.
Possible mitigations for customers (not true workarounds to the bug itself):
- Access control: Strictly limit who can manage automation rules and who can use API tokens capable of calling the Automation Rule Management API.
- Process control: Treat any exports from this API as highly sensitive and implement a custom redaction step (e.g. stripping or masking authorization headers and webhook URLs) before storing or sharing the exported JSON.
- duplicates
-
AUTO-2207 Automation Rule Management API returns sensitive values in clear text in Jira Cloud
-
- Closed
-